Current web3 wallet key management landscape and how MPC is reshaping it?

5 mins
Last Edited: Aug 25, 2023
Share
Current Web3 wallet key management landscape and how MPC is reshaping it?
Insights into the current paradigm of key management in Web3 wallets
Web3 Wallets
Key Management
Intermediary
With the recent collapse of FTX, centralized exchanges as 'custodians' have failed to provide users with actual ownership over their cryptos.
This has piqued a lot of interest in MPC technology.
Why?
Because MPC has some exciting applications that can make your crypto wallets even more 'SECURE'!
Few reasons why people are eager to shift to MPC technology -
First, traditional custodial wallets rely on a single private key for access, making them the potential point of a single failure.
Second, conventional wallets, especially those offered by centralized exchanges or custodial services, store private keys on centralized servers. This concentration of keys is prone to cyberattacks
Here's the key insight:
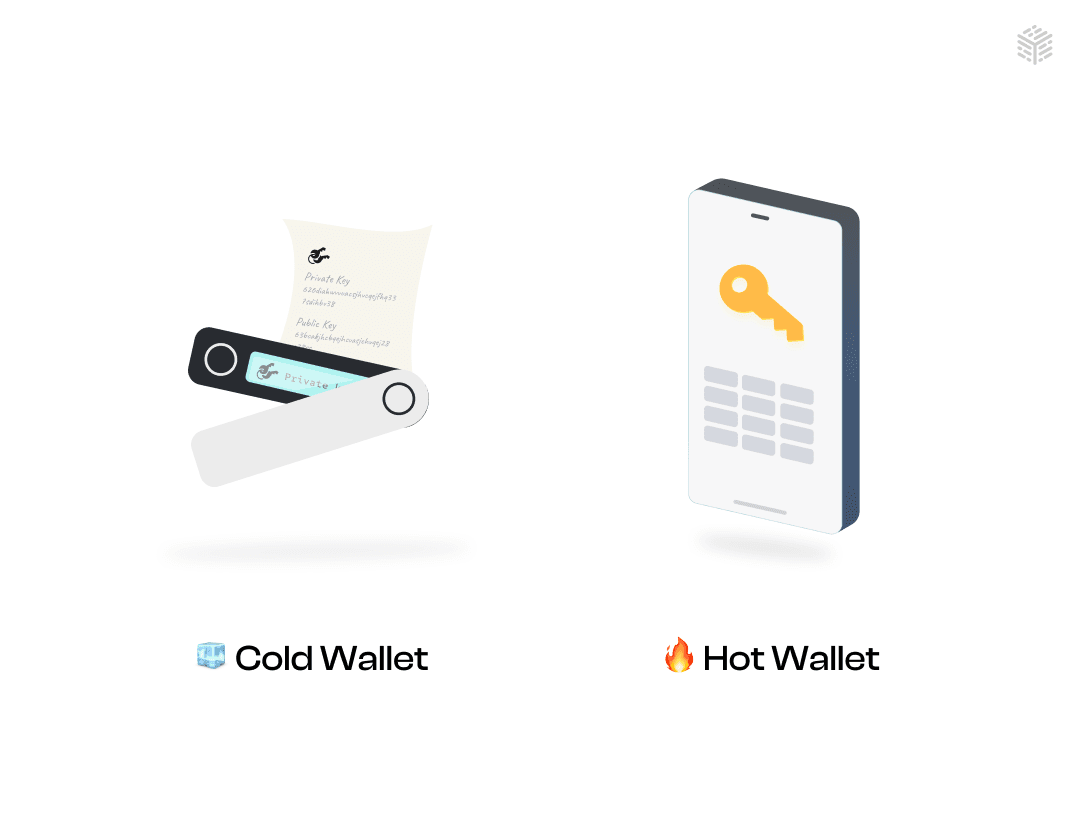
When we look at the current landscape of custodial wallets , it is divided into two distinct categories – hot wallets and cold wallets.
| Hot Wallets | Cold Wallets |
|---|---|
| Hot wallets encompass a variety of cryptocurrency wallets ( Metamask, TrustWallet, Frontier Wallet, and Exodus Wallet) accessible through internet-connected devices. This includes desktop wallets, mobile wallets, and even wallets provided by exchanges. | Cold wallets (hardware, paper wallets) represent a form of crypto storage that prioritizes security. They keep your private keys offline, completely detached from the internet. |
| These wallets offer convenience for day-to-day transactions, allowing swift access to your assets. However, the trade-off lies in their security vulnerability. Since your private keys are exposed to potential online threats such as hacking or malware attacks, there's an inherent risk involved. | While they might be less convenient for everyday transactions since you'll have to import keys to an online device when required, they provide robust security against online threats. |
Whenever you examine a hot wallet or a self-custodial wallet like MetaMask, two vital factors should always be taken into consideration-
- Key Storage: How are those private keys actually stored in the wallet?
- Access and Control: Whether you have direct access and control over these keys?
These two factors are intricately intertwined and play a pivotal role while evaluating the functionality and security of a wallet.
This article seeks to provide you with insights into the current paradigm of key management in self-custodial Web3 wallets-
Let's take a closer look at the crypto wallet spectrum to get a comprehensive understanding-| Custody | Types | |
|---|---|---|
| Self-Custody | Non Distributed Self-Custody | Distributed Self-Custody |
| Shared-Custody | Enterprise Shared Custody | P2P Shared Custody |
| Delegated Custody | Designated non distributed custody | Designated distributed custody |
A. Self-Custody:
When you use self-custody wallets, you have perpetual access and control over your digital assets. The great thing is, the self-custody wallet service provider can't hold you back from exporting your wallet or switching to another one. Whether the private keys are stored in their entirety or distributed among multiple parties (such as in MPC wallets), users retain absolute control over their keys. This control is crucial for securing their assets against unauthorized access.You're always in the driver's seat!
This is further subdivided in two parts -
| Non Distributed Self-Custody | Distributed Self-Custody |
|---|---|
| A non-distributed self-custodial wallet is a wallet where the entire responsibility of storing and controlling private keys lies with a single location or device. This setup can offer convenience but might carry a higher risk if that single point of control is compromised, such as loss or theft of the private key. | A distributed self-custodial wallet refers to a type of wallet where the responsibility of storing and managing private keys is spread across multiple locations or devices. This approach enhances security by reducing the risk of a single point of failure. It's like having backup keys in different places. |
| Hardware or paper wallets are the real life examples of several types of non distributed self-custodial wallets. | MPC-TSS wallets - Zengo, Jade , Unipass, Particle network are the real life examples of the distributed self custodial wallets. |
B. Shared-Custody:
Under some approaches, wallets are linked to distributed key shares that are divided among the user, the wallet provider (or a group of enterprises), or a group of guardians. To perform actions like generating signatures, a minimum number of these parties need to come together and participate, either at the same time or independently. Alternatively, multi-sig smart contract wallets can also involve a minimum number of affiliated guardians to validate transactions. This adds an extra layer of security and flexibility to the wallet setup.
This is further subdivided in two parts -
| Enterprise Shared Custody | P2P Shared Custody |
|---|---|
| In this setup, signatures in wallets involves sharing key shares between phone wallets, enterprise servers, cloud services, or storage. | In this setup, signing authorities, which allow transactions to be authorized and executed, are divided among the peers. Each peer holds a portion of the private key or a unique key share and come together to execute the transaction. |
| Zengo and Coinbase are real life examples that have significantly improved security compared to traditional wallets relying solely on seed phrases and single private keys. | Examples of P2P Shared Custody wallet implementations include social multi-sig wallets like Gnosis SAFE and custody solutions based on Multi-Party Computation (MPC). |
C. Delegated Custody:
Delegated Custody is another method in which the management of keys or key shares is entrusted to external entities- ‘delegated enterprises or a network’. In this setup, user delegate the control and storage of their private keys to these external entities. A common example is when users hold their digital assets on centralized exchanges.
This is further subdivided in two parts -
| Designated non distributed custody | Designated distributed custody |
|---|---|
| The key responsibility for holding and managing the private keys or access to the digital assets is entrusted to a one specific delegated enterprise or a network. | The key responsibility for managing the private key is shared or access to digital assets is distributed among a group of enterprises or nodes. |
| BitGo , Free wallet are few examples of designated non distributed custody | Coinbase, Free wallet are few examples of designated distributed custody |
The current state of private key storage in crypto wallets raises concerns due to the challenges and risks associated with each category. While self-custody provides maximum control, the entire key is locally stored on your device, which means if you lose access to your device for any reason, you lose access to your wallet. Thus, your device becomes a single point of failure (SPOF). On the other hand, shared custody and delegated custody introduce complexities around trust, reliance on third parties, and potential vulnerabilities.
What if your self-custody wallet not only supercharges security but also takes away the hassle of remembering, storing, and protecting private keys?
Exactly! This is where the concept of Multi-Party Computation (MPC) comes into the picture, where you, as a user of a self-custodial wallet- distribute your private keys among several trusted devices.
Conclusion
To sum up, the idea of "distributed - self custody" is the ideal spot in managing digital assets at both enterprise and retail level . By dispersing ownership or control of private keys among multiple entities, the risks associated with a single point of failure is reduced.
This concept stands in contrast to shared and delegated custody , which have demonstrated vulnerabilities in real-world use cases.
Whereas, distributed self-custody approach resonates with the core principles of decentralization, security, and individual empowerment that form the cornerstone of the entire crypto industry.
The next article discusses different methods of securing digital assets while also highlighting how innovative wallet solutions rooted in MPC (Multi-Party Computation) and TSS (Threshold Signature Schemes) have opened pathways towards adoption of distributed self-custody.
</div>
References
https://medium.com/silence-laboratories/redefining-nomenclature-of-custody-81ee28f20731
🔑 Key Takeaway
The self-custody approach empowers users with perpetual control, with MPC-backed distributed self-custody mitigating single points of failure. The shift towards distributed self-custody, empowered by MPC, emerges as a key paradigm for safeguarding digital assets.